How Does SKAN Work?
- Thursday, November 30th, 2023
- Share this article:
Grant Simmons, VP, Kochava Foundry, explains how the firm’s Ultimate Marketer’s Guide to SKAdNetwork (SKAN) can help marketers navigate Apple privacy-centric ad attribution framework.
 In the evolving landscape of digital advertising, privacy has taken center stage. Apple’s SKAdNetwork (SKAN) framework is a testament to this shift, presenting new challenges and opportunities for marketers navigating the iOS ecosystem. As experts in data-driven marketing, Kochava Foundry is dedicated to guiding marketers through this new terrain, ensuring you can harness the power of SKAN to drive successful campaigns while respecting user privacy.
In the evolving landscape of digital advertising, privacy has taken center stage. Apple’s SKAdNetwork (SKAN) framework is a testament to this shift, presenting new challenges and opportunities for marketers navigating the iOS ecosystem. As experts in data-driven marketing, Kochava Foundry is dedicated to guiding marketers through this new terrain, ensuring you can harness the power of SKAN to drive successful campaigns while respecting user privacy.
SKAN, Apple’s solution for privacy-centric ad attribution, has emerged as a crucial tool for marketers in the post-IDFA era. As a privacy-enhancing technology (PET), SKAN allows for campaign measurement that respects user privacy, offering a path forward in a world where traditional tracking methods are becoming less feasible. Understanding SKAN and integrating it into your marketing strategies is now more important than ever, but can be complicated without the right resources
The Ultimate Marketer’s Guide to SKAdNetwork (SKAN) was created by Kochava to offer a comprehensive overview of SKAN, from its inception to its latest updates. The free guide unpacks the complexities of SKAN, covering how it works, why it matters, and how to leverage it effectively. It takes you under the hood of SKAN, demystifying its mechanisms and showing you how to navigate its intricacies. We’ll dig into some of those answers below.
The question of how SKAN (SKAdNetwork) works is not an easy one to answer. In fact, the complexity of its functionality increases with each new version. However, by deconstructing its intricate processes into comprehensible steps, understanding how SKAN works becomes a little easier. The following flow diagrams will help you establish a robust grasp of SKAN’s operational framework, thereby enhancing your readiness to effectively harness this privacy-enhancing technology.
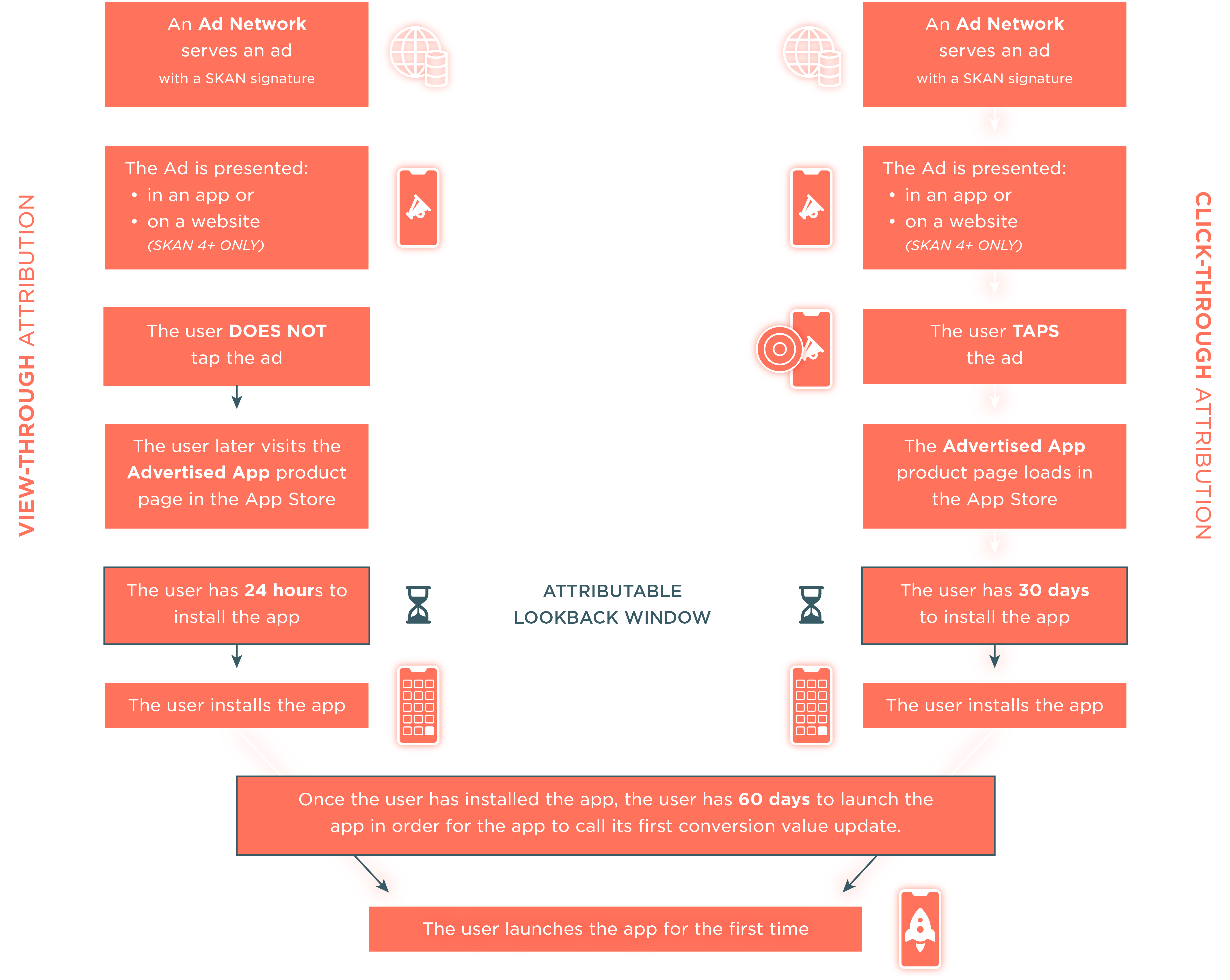
SKAN diagram 1: Ad Network serving an ad through a user’s first app launch
The left side of the diagram explains view-through attribution, when the user DOES NOT click on an ad. The right side explains click-through attribution, when the user DOES click on an ad.
As you can see, steps 1 and 2 of each flow start off the same – an ad network serves an ad, and the ad is presented in an app or website (starting with SKAN 4). Depending on the user’s action (no click or click), the attribution lookback window drastically changes. With a click, the user has a longer time (up to 30 days) to install the app, while they only have 24 hours if they only view the ad. The intent of a click holds a heavier weight and offers more time for attribution to be awarded.
If the app is installed within the attribution window, the user then has 60 days to launch the app for the app to call its first conversion value update.
Once the user launches the app for the first time, the process that follows is quite different between SKAN 2-3 vs SKAN 4. As such, we will unpack them differently.
SKAN diagram 2: Post app launch on SKAN 2-3
At this point, the app has been downloaded but has yet to be opened. For SKAN versions 2-3, when the user launches the app for the first time, a timer starts (24 hours). The left side flow demonstrates when no conversion takes place (eg, the user opens the app but does not complete any in-app action which results in a conversion value update). The right side shows when an in-app action takes place, triggering a conversion value update call. When this happens, the 24 hour timer restarts and will continue to reset until (A) a lack of user interaction, (B) an end of conversion value range, or (C) a forced stop in the app.
As soon as the second timer expires in either flow (left or right), the privacy threshold is applied and the install validation postback is sent to the ad network. When the ad network receives the postback, it is then forwarded to the advertised app’s mobile measurement partner (MMP) with any necessary campaign metadata mapping appended.
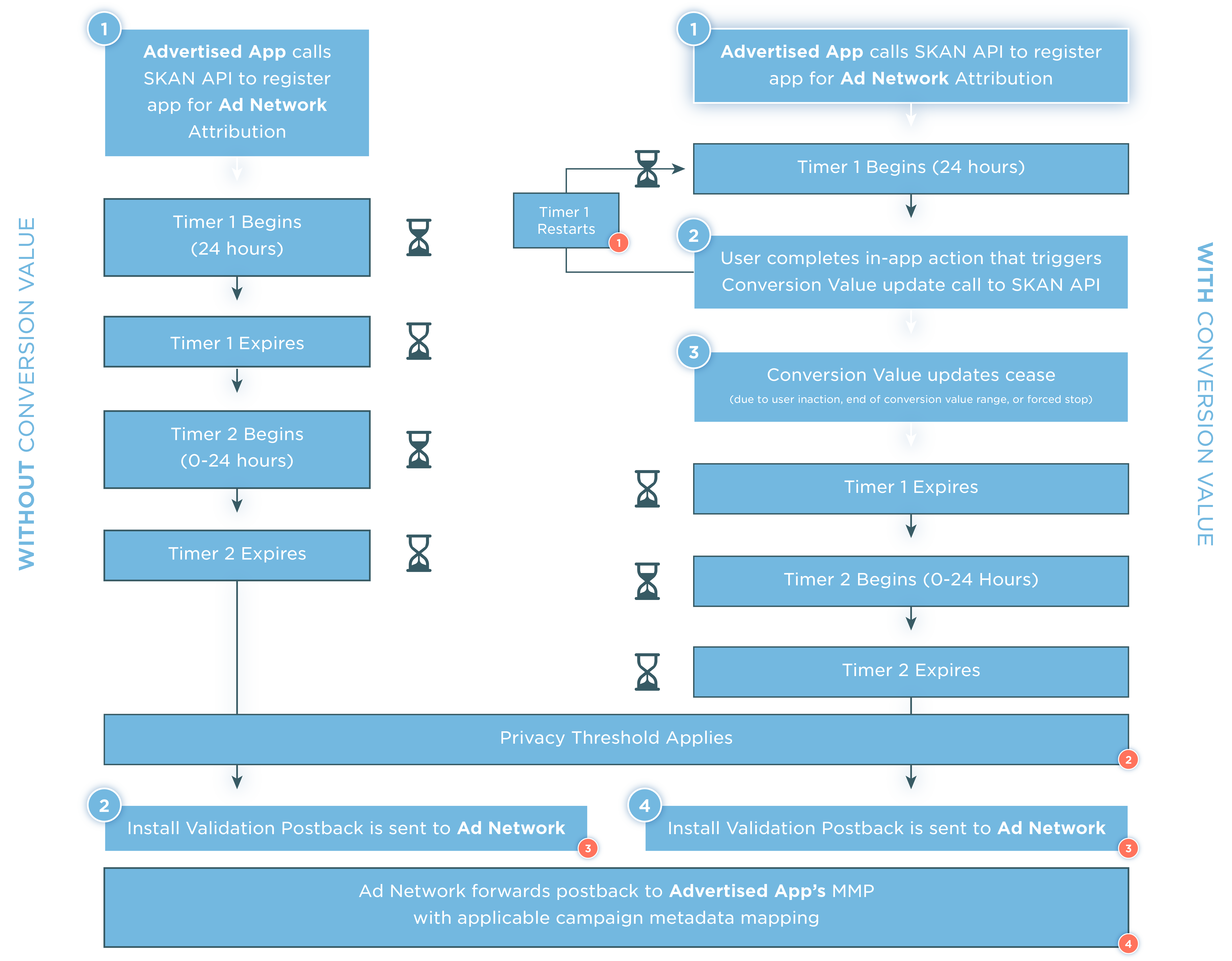
About SKAN timers
Apple uses timers in SKAN to randomize responses to ad networks and advertisers—a mechanism to obfuscate data and prevent re-identification of individual users or devices.
About SKAN privacy thresholds
To protect user privacy, Apple applies minimum privacy thresholds before sending any postbacks.
Additionally, Apple may redact certain values (e.g. source app ID, conversion value) from postbacks that are sent if a certain volume of conversions aren’t reached. The exact privacy thresholds are not publicly known.
About SKAN postbacks
Beginning in SKAN 3, Apple added the ability for influencing ad networks (not just the ad network that won attribution) to receive a postback. This enabled multi-touch attribution insights in SKAN for the first time. Additionally, Apple added the ability for advertisers to receive their own copy of postbacks, as opposed to the ad networks being the sole recipient.
About SKAN campaign metadata mapping
In SKAN versions 2-3, ad networks are confined to the use of campaign ID values (0-99). However, to gain a more detailed view beyond just campaign-level insights, ad groups, ad sets, and other campaign variables can be mapped to the different digits. This approach allows for a more granular understanding of campaign performance. An MMP plays a crucial role in this process by decoding this information across integrated partners, thereby enabling standardized reporting for the advertiser.
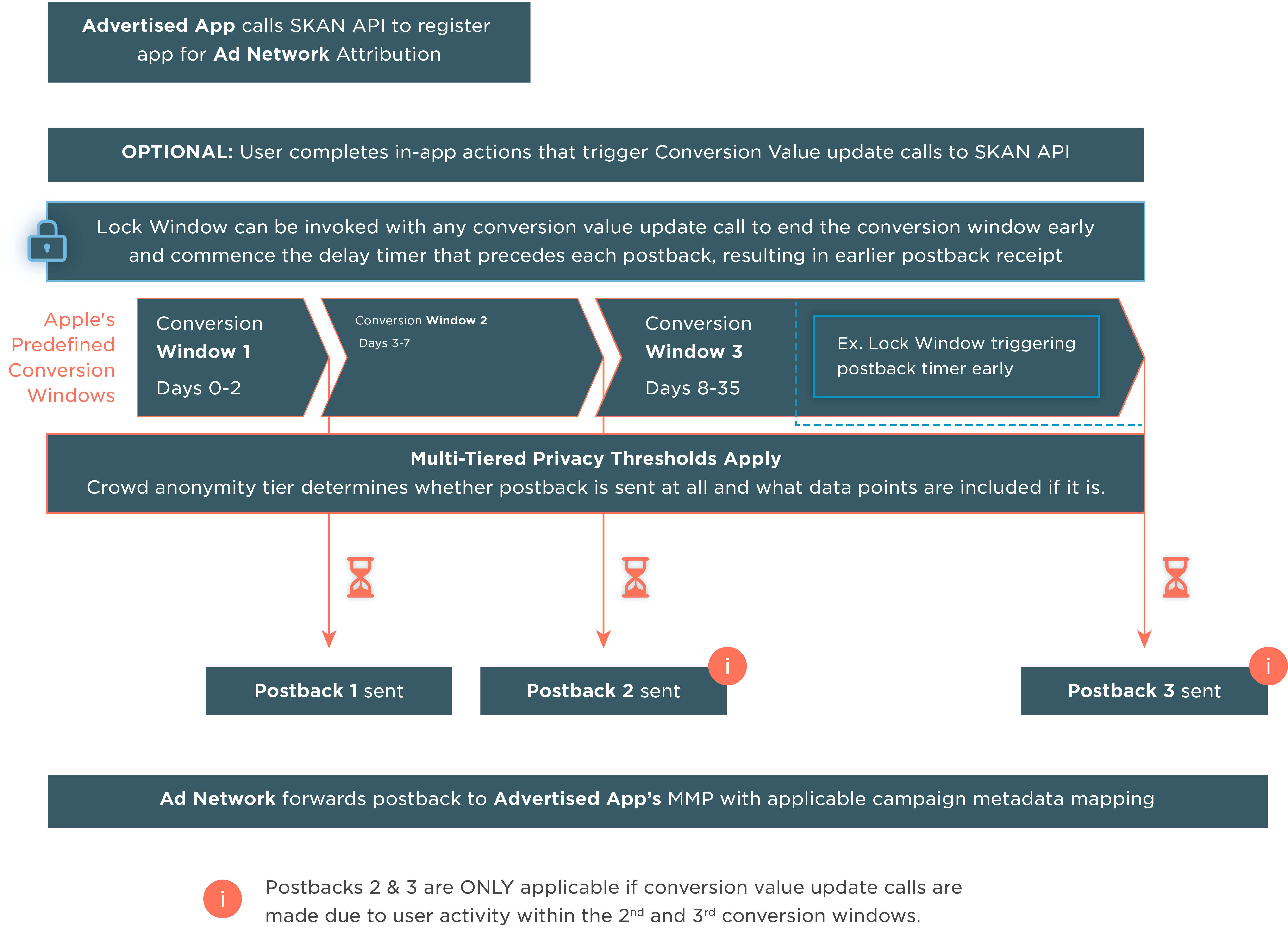
SKAN diagram 3: Post-app launch on SKAN 4+
The final diagram illustrates the post-app launch on SKAN version 4+. SKAN 4 brought forth several noteworthy updates for Apple, most notably the inclusion of multiple postbacks across three predetermined conversion windows. This extension offers ad networks and advertisers a substantially longer period to observe user behavior and assess post-installation quality. This stands in contrast to the single conversion postback option provided by SKAN versions 2-3.
Continue learning
SKAN is not an easy topic to digest and it becomes even more difficult when the mechanisms change with each new version. On SKAN 4+ in particular, crowd anonymity in conjunction with the conversion window, impacts several postback data points. These include:
- Source App ID or Source Web Domain
- Source Identifier
- Conversion Value
There are also changes to the privacy thresholds with SKAN 4+. Similar to previous versions, an initial, minimum volume threshold must be reached to receive any postbacks. However, after that initial volume threshold is reached, postbacks will be received, but the granularity of data points included in the postback will be dependent on four tiers of crowd anonymity.
At Kochava Foundry, we believe in empowering marketers with the tools and knowledge they need to thrive in a privacy-first world. That’s why we offer SKAd Consult, a specialized service designed to help you optimize your SKAN setup. Our team of experts will provide you with a deep dive into your current SKAN model, events, and setup, identifying opportunities for optimization.
As the digital advertising landscape continues to evolve, the challenges posed by increasing privacy protections are likely to grow. Finding answers and achieving marketing success in this new environment may seem daunting. However, with the right guidance, these challenges can be transformed into opportunities for growth and innovation.
If you would like to learn more about these changes, gain more in-depth knowledge from The Ultimate Guide to SKAdNetwork (SKAN), free to download here.